5-Tier Risk Framework for Mitigating Human Error

Most security incidents still start with a person: a rushed click, a reused password, a file sent to the wrong place. For years, the default answer has been “more awareness training,” but that treats every employee as the same level of risk and ignores the environment they work in. A better approach is to treat […]
Zero Trust Meets the Real World Network: From VPN and Vibes to Measured Trust

How business leaders and their MSPs can move from flat, fragile networks to smaller blast radiuses in 90 days — without ripping everything out. In slide decks, zero trust is all glass towers and pristine diagrams. In the real world, it looks more like an old castle that’s been expanded badly — new wings slapped […]
Hiring an Attacker: Deepfake Employees, Fake Résumés, Real Breaches
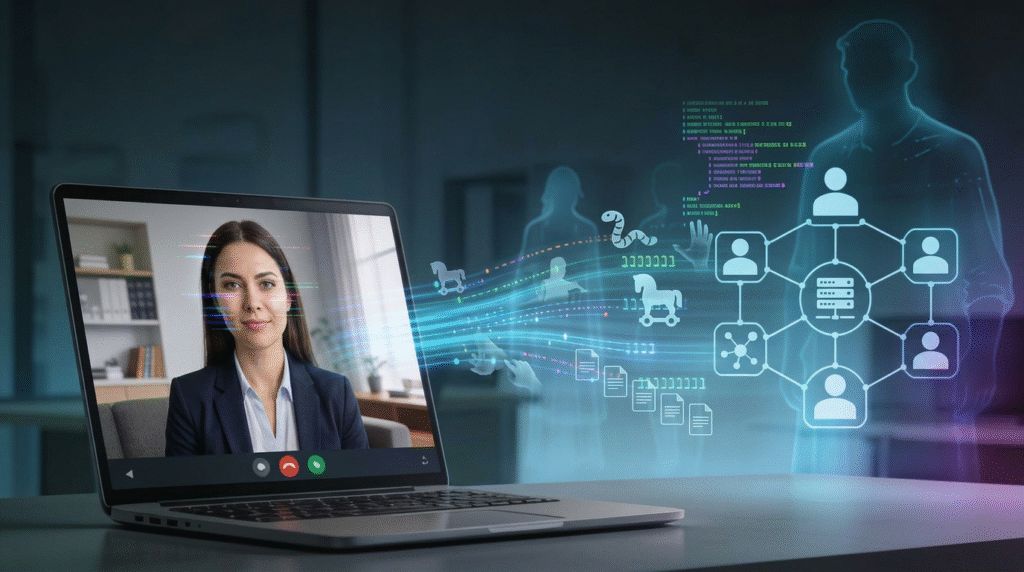
Hiring a fully remote “cloud engineer” felt like a win. The résumé checked every box, the video interviews were smooth, the references came back glowing. The new hire shipped code quickly, asked smart questions in Slack, and never missed a stand‑up. Thirty days later, incident response found a quiet backdoor in the CI/CD pipeline and […]
The New Breach Supply Chain: When Your Data Broker Gets Pwned
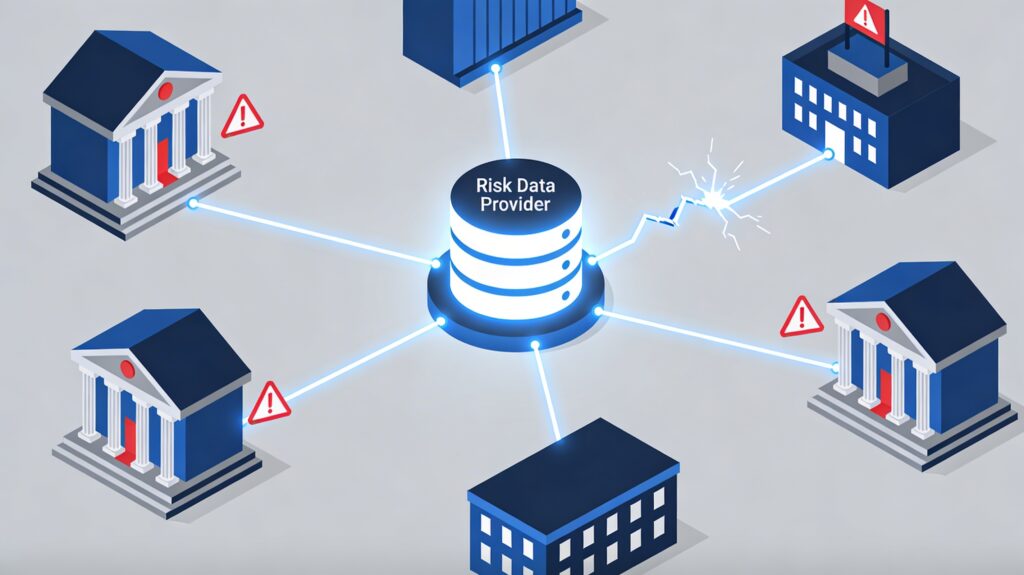
When your supply chain gets breached, you inherit its chaos, whether you like it or not. The LexisNexis incident and a wave of third‑party breaches in 2026 are a warning shot for every legal, risk, and engineering leader who leans on data brokers to keep their business compliant and fraud‑resistant. When Your Data Provider Makes […]
Inside the Conduent Mega-Breach: What a “Largest in U.S. History” Incident Teaches About Third‑Party Risk
When a contractor you barely name in board meetings leaks Social Security and health data for at least 25 million people, it stops being “their” incident and becomes a referendum on your third‑party risk program. The Conduent breach is exactly that kind of stress test. When your outsourcer becomes the soft underbelly Conduent, a New […]
Turning a Free Risk Assessment Into Your Client Security Language (Not Just a Compliance Check)

Most MSPs don’t have a language problem with security; they have a translation problem. The Blacksmith Free Risk Assessment gives you a single, reusable grammar you can use to talk about both compliance and security with non‑technical clients in a way that sticks. The problem: no shared language with clients When you walk into a QBR and start talking […]
Operational Ransomware: When Uptime Becomes the Real Crown Jewel

Ransomware is increasingly about stopping a business from functioning, not just stealing or encrypting files. The sectors feeling this most acutely are healthcare, manufacturing, managed service providers, and critical services where every minute of downtime carries a real human or economic cost. When “just” data loss isn’t the point In today’s big-game ransomware operations, the […]
KEV-Driven Patching and “Emergency Directive Fatigue”
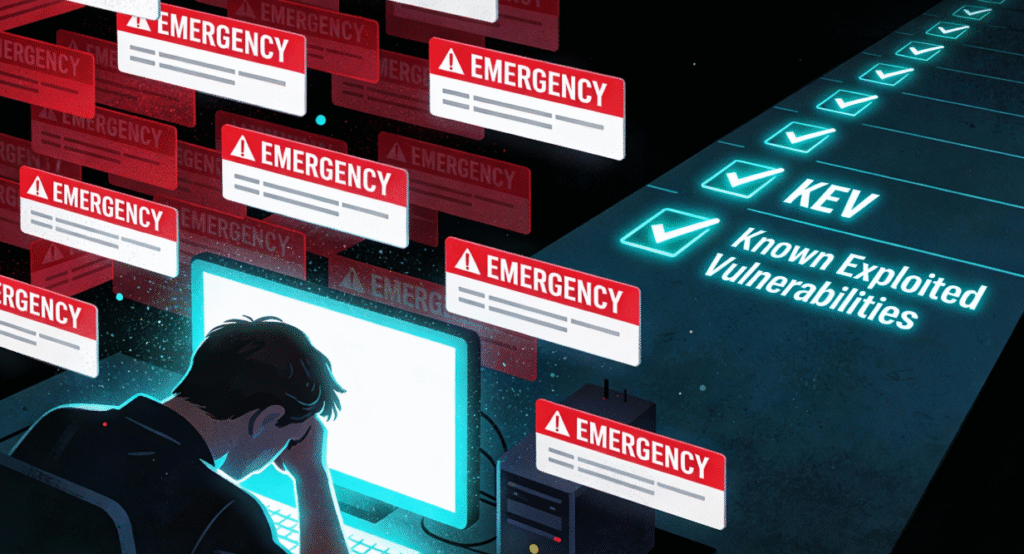
Stop chasing every CVE headline; build a KEV-first, risk-based patch playbook If it feels like you’ve been living in a permanent “drop everything and patch” sprint for the last five years, you’re not imagining it. Every week ships a new “critical” CVE, a vendor blast, and at least one headline implying that if you don’t patch […]
The 2026 MSP: AI Threats, Business Risk, and the New Model for Growth

Managed services are heading into one of the most important transitions in their history. AI‑driven attacks are accelerating, cyber insurance is tightening, regulators are raising expectations, and clients are less interested in tickets closed than in risk reduced and revenue protected. For MSPs, 2026 is not just another planning cycle; it is a structural reset […]
The Hidden Compliance Crisis: Shadow AI in the Workplace

As artificial intelligence reshapes business operations, one of the most pressing yet underappreciated compliance risks is the rise of Shadow AI — employees using unsanctioned AI tools without organizational oversight. From ChatGPT-style assistants and automated copilots to image generators and workflow agents, these tools have infiltrated workplaces at astonishing rates. According to Microsoft’s 2025 Work Trend […]
