MFA Bypass Kits, AI Phishing, and the End of ‘Good Enough’ Authentication

MFA used to be the control that let MSPs and security pros sleep at night. In 2026, industrial‑grade phishing kits and AI email engines have turned “we turned on MFA” into the new “we installed antivirus” — expected, but nowhere near enough. When MFA stops saving you Picture the pattern you’ve seen in too many […]
Inside the Conduent Mega-Breach: What a “Largest in U.S. History” Incident Teaches About Third‑Party Risk
When a contractor you barely name in board meetings leaks Social Security and health data for at least 25 million people, it stops being “their” incident and becomes a referendum on your third‑party risk program. The Conduent breach is exactly that kind of stress test. When your outsourcer becomes the soft underbelly Conduent, a New […]
CMMC by Stealth: How GSA Is Sneaking NIST 800‑171 Into Civilian Contracts
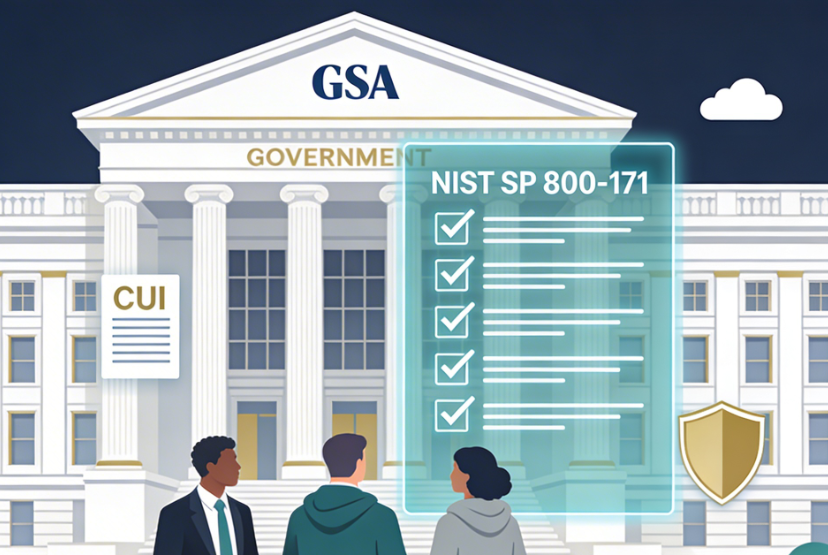
GSA is turning NIST 800‑171 into a de facto requirement for civilian contractors, even without a formal CMMC program — especially anywhere Controlled Unclassified Information (CUI) touches your systems. For small and mid-size firms, that means “good enough IT” is no longer compatible with keeping GSA work. The stealth rollout: CMMC without the brand GSA […]
Security Reporting Rules Are Coming for Everyone: How MSPs and vCISOs Prepare Clients for CISA‑Grade Incident Disclosures

The era of “optional” cyber incident reporting is ending, and the operational burden is going to land squarely on managed security providers and vCISOs. CISA is actively refining cyber incident and ransom‑payment reporting rules under CIRCIA, reopening comments, and launching town halls with critical infrastructure sectors to stress‑test what’s realistic. Even if many of your […]
From Alerts to Action: Teaching Execs to Read Cyber Risk Like a Weather Report

Executives are drowning in cyber alerts and starving for decisions. If you want their support, your job isn’t to forward every CVE — it’s to turn threat noise into something they can read like a weather report: clear, comparable, and decision‑ready. What Executives Actually Need (And Don’t) The SOC lives in logs, CVEs, and vendor […]
When Ransomware Becomes a Civic Emergency: What Cities Must Learn from St. Paul

When ransomware hits a city, it stops being an IT story and becomes a public safety problem. In 2025, St. Paul, Minnesota gave us a template for what that escalation looks like. When “IT Outage” Turns into a State of Emergency On July 25, 2025, St. Paul began detecting suspicious activity on its internal networks, […]
Zero-Click Visibility: Securing a Brand When No One Ever Hits Your Site

We’re fast approaching a time when most of your prospects will never land on a site you manage — and that’s a security problem you can’t patch with an agent install. When a CFO types “Is [Client]’s backup provider secure?” or “Best cybersecurity for a 50‑person firm” into Google or an AI assistant, they get […]
Operational Ransomware: When Uptime Becomes the Real Crown Jewel

Ransomware is increasingly about stopping a business from functioning, not just stealing or encrypting files. The sectors feeling this most acutely are healthcare, manufacturing, managed service providers, and critical services where every minute of downtime carries a real human or economic cost. When “just” data loss isn’t the point In today’s big-game ransomware operations, the […]
KEV-Driven Patching and “Emergency Directive Fatigue”
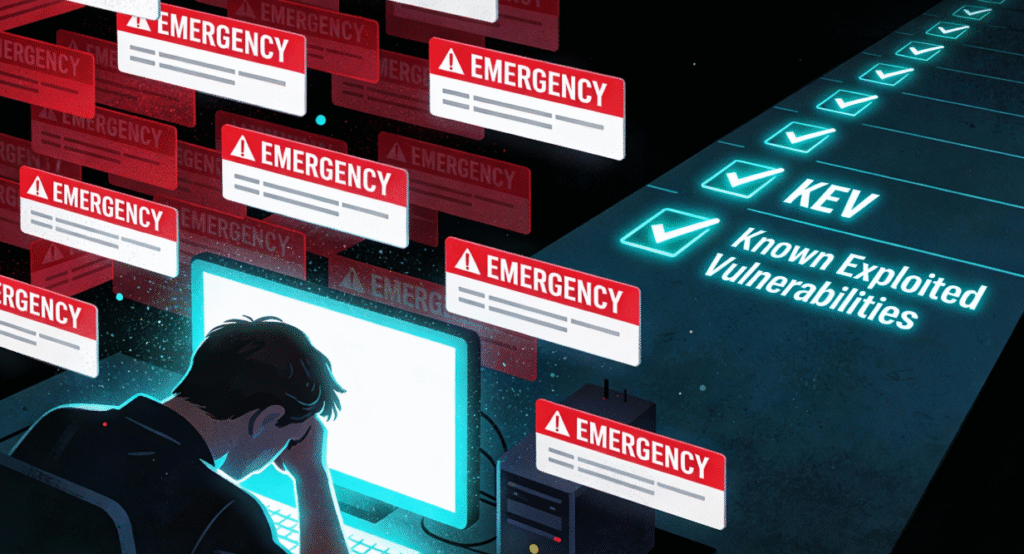
Stop chasing every CVE headline; build a KEV-first, risk-based patch playbook If it feels like you’ve been living in a permanent “drop everything and patch” sprint for the last five years, you’re not imagining it. Every week ships a new “critical” CVE, a vendor blast, and at least one headline implying that if you don’t patch […]
Building a Digital Trust Architecture: Moving Beyond Isolated Controls

We’ve said it (and you’ve heard it) many times now: digital trust has become table stakes for doing business. At its core, digital trust is the confidence that systems, data, and interactions are secure, reliable, and respectful of users and their rights. As organizations lean into AI, automation, and always-on digital services, they need more […]
