The MSP “Trust Surface”: Identity, VPNs, and Tenant Isolation as Your Real Perimeter

Most MSPs don’t get popped because of some cinematic zero‑day. They get popped because one technician’s credentials are phished, a shared VPN drops them into a flat client network, and their tools do exactly what they were designed to do — only under an attacker’s control. The real perimeter isn’t the firewall anymore; it’s your […]
When 3,322 Breaches Is “Normal”: Why Boards Are Failing Cyber Governance

In 2025, the United States set a new record: 3,322 reported data compromises in a single year. That is not a typo, and it is not an outlier — it is the third year in a row with more than 3,000 incidents and a 79% increase in breaches over the past five years. For all […]
Whoops! What We Can Learn from South Korea’s $4.8m Crypto Key Blunder

Officials in South Korea’s National Tax Service stood behind a table of seized hardware wallets prepping for their victory lap — cameras rolling, proud to show the public that crypto‑enabled tax dodging had consequences. The photos went out in high resolution. On social media, people zoomed in — and found the handwritten seed phrase for […]
OAuth Abuse Is the New Phishing: Why “Log In With X” Keeps Burning You
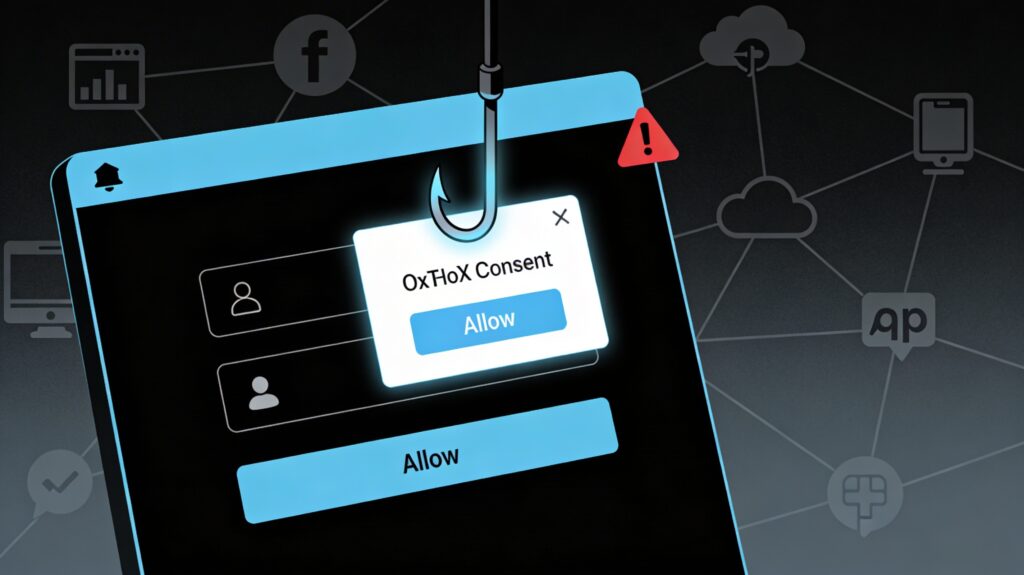
OAuth abuse has quietly become the phishing technique that slips past your MFA, your “security‑aware” users, and your cloud email filters. Recent campaigns abusing OAuth redirects and malicious apps in Microsoft Entra ID and Google Workspace show that “Log in with X” is now one of the easiest ways into your SaaS estate. Phishing Without […]
Building a Digital Trust Architecture: Moving Beyond Isolated Controls

We’ve said it (and you’ve heard it) many times now: digital trust has become table stakes for doing business. At its core, digital trust is the confidence that systems, data, and interactions are secure, reliable, and respectful of users and their rights. As organizations lean into AI, automation, and always-on digital services, they need more […]
Turn Compliance Into a Core MSP Offering, Not an Add-On

Compliance Is the New Growth Engine For years, most MSPs treated compliance like an annoying side quest: something you help with begrudgingly when a client’s cyber insurer or auditor sends over a questionnaire. That model is breaking down. Buyers are no longer satisfied with “we keep things patched” as an answer when their board, regulator, […]
Why Security Culture Beats Security Tools (And Makes Them Worth What You Paid)

Security culture beats security tools because tools only amplify the behavior you already have. A great stack in the hands of a rushed, over‑pressured organization just turns bad habits into faster, louder failures. A modest stack inside a culture that takes security seriously will almost always outperform it. Breached with everything “turned on” Picture the […]
Building A “Green IT” Offering Your SMB Clients Will Actually Pay For

Green IT has shifted from “nice to have” to a buying criterion, especially for younger, growth‑minded SMBs. Sustainability is now showing up in MSP trend reports as both a differentiator and a way to justify premium service tiers when it is tied directly to cost savings and risk reduction. Why SMBs Will Pay For Green […]
Always-On, Always At Risk: MSP Mental Health in the Age of 24/7 Incidents

MSPs are carrying more risk than ever, and it is not just technical. Chronic stress, 24/7 expectations, and nonstop incidents are turning mental health into a frontline security issue. When an MSP’s people are exhausted, clients are less safe. The always-on reality of MSP work MSPs live in a world of middle-of-the-night alerts, demanding SLAs, […]
It Takes More Than Policies — Building a Resilient Compliance Culture

Most organizations have compliance policies. Yet with compliance and risk constantly changing these days, policies alone don’t create a culture that can withstand regulatory scrutiny, reputation shocks, or evolving threats. To deliver true business resilience, compliance must be lived by every team, championed daily by leadership, and woven into the operational fabric of every department. […]
