5-Tier Risk Framework for Mitigating Human Error

Most security incidents still start with a person: a rushed click, a reused password, a file sent to the wrong place. For years, the default answer has been “more awareness training,” but that treats every employee as the same level of risk and ignores the environment they work in. A better approach is to treat […]
Zero Trust Meets the Real World Network: From VPN and Vibes to Measured Trust

How business leaders and their MSPs can move from flat, fragile networks to smaller blast radiuses in 90 days — without ripping everything out. In slide decks, zero trust is all glass towers and pristine diagrams. In the real world, it looks more like an old castle that’s been expanded badly — new wings slapped […]
Whoops! What We Can Learn from South Korea’s $4.8m Crypto Key Blunder

Officials in South Korea’s National Tax Service stood behind a table of seized hardware wallets prepping for their victory lap — cameras rolling, proud to show the public that crypto‑enabled tax dodging had consequences. The photos went out in high resolution. On social media, people zoomed in — and found the handwritten seed phrase for […]
Hiring an Attacker: Deepfake Employees, Fake Résumés, Real Breaches
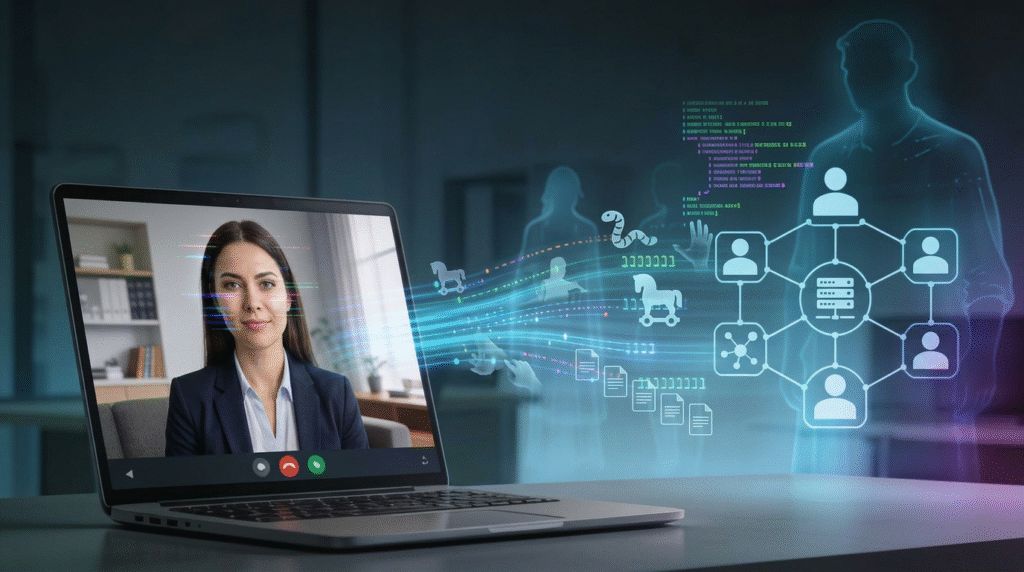
Hiring a fully remote “cloud engineer” felt like a win. The résumé checked every box, the video interviews were smooth, the references came back glowing. The new hire shipped code quickly, asked smart questions in Slack, and never missed a stand‑up. Thirty days later, incident response found a quiet backdoor in the CI/CD pipeline and […]
OAuth Abuse Is the New Phishing: Why “Log In With X” Keeps Burning You
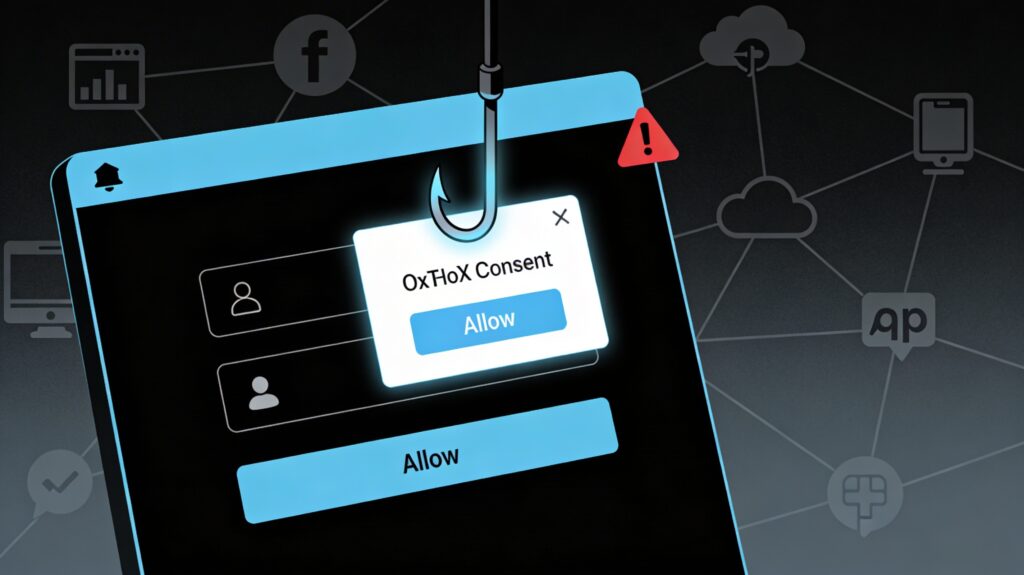
OAuth abuse has quietly become the phishing technique that slips past your MFA, your “security‑aware” users, and your cloud email filters. Recent campaigns abusing OAuth redirects and malicious apps in Microsoft Entra ID and Google Workspace show that “Log in with X” is now one of the easiest ways into your SaaS estate. Phishing Without […]
The New Breach Supply Chain: When Your Data Broker Gets Pwned
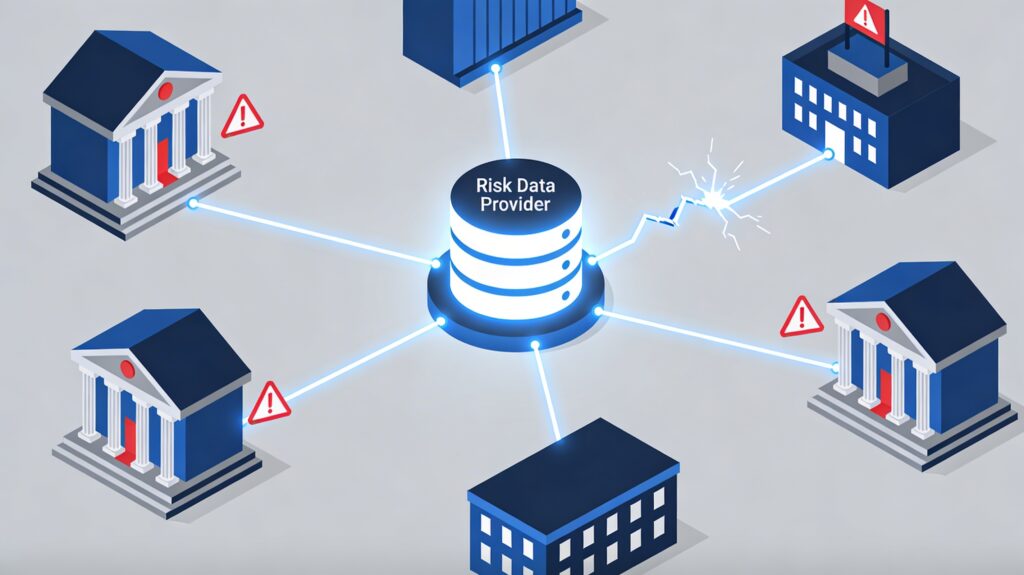
When your supply chain gets breached, you inherit its chaos, whether you like it or not. The LexisNexis incident and a wave of third‑party breaches in 2026 are a warning shot for every legal, risk, and engineering leader who leans on data brokers to keep their business compliant and fraud‑resistant. When Your Data Provider Makes […]
MFA Bypass Kits, AI Phishing, and the End of ‘Good Enough’ Authentication

MFA used to be the control that let MSPs and security pros sleep at night. In 2026, industrial‑grade phishing kits and AI email engines have turned “we turned on MFA” into the new “we installed antivirus” — expected, but nowhere near enough. When MFA stops saving you Picture the pattern you’ve seen in too many […]
Inside the Conduent Mega-Breach: What a “Largest in U.S. History” Incident Teaches About Third‑Party Risk
When a contractor you barely name in board meetings leaks Social Security and health data for at least 25 million people, it stops being “their” incident and becomes a referendum on your third‑party risk program. The Conduent breach is exactly that kind of stress test. When your outsourcer becomes the soft underbelly Conduent, a New […]
CMMC by Stealth: How GSA Is Sneaking NIST 800‑171 Into Civilian Contracts
GSA is turning NIST 800‑171 into a de facto requirement for civilian contractors, even without a formal CMMC program — especially anywhere Controlled Unclassified Information (CUI) touches your systems. For small and mid-size firms, that means “good enough IT” is no longer compatible with keeping GSA work. The stealth rollout: CMMC without the brand GSA […]
Compliance Debt Is the New Tech Debt: Surviving 2026’s Layered Cyber Regulations
Compliance debt is the pile‑up of half-implemented controls, untested policies, and missing evidence that builds as new regulations land faster than teams can operationalize them. In 2026, SEC exam priorities, NIS2, and AI-governance rules are turning that debt into a real balance sheet risk for security leaders. What “compliance debt” really is Like tech debt, compliance debt […]
