Vendor Risk, Fake Automation, and the Green Check Trap
A vendor questionnaire is not vendor risk management. It’s a starting point. Sometimes a useful one. But if your process ends with a filled-out form and a SOC report in a folder, you’re not managing risk — you’re documenting optimism. In this Get NIST-y, Jared and Mike use the Mythos supply chain mess to highlight […]
AI is Useful. AI Slop Is Not.
AI is everywhere right now — and if you’re running an MSP, you’re feeling it from every direction. Your PSA has AI. Your RMM has AI. Your documentation platform has AI. Your quoting tool probably has AI. At this point, we’re all just waiting for the coffee maker to start summarizing tickets. But here’s the […]
Blacksmith Wins 2026 Q1 Category Leader Award!

Blacksmith just earned another BetterTracker (Channel Program) Category Leader badge for 2026 Q1 — our latest quarter ranked among the top‑rated vendors in the IT channel across more than 80 technology categories. Blacksmith’s 2026 Q1 Category Win For 2026 Q1, Blacksmith was recognized as a Category Leader in Compliance. That means MSPs and IT providers […]
Higher‑Level Advisory Services Your MSP Should Be Monetizing

Most MSPs still sell themselves as “outsourced IT” or “24/7 support.” That message is increasingly out of step with what growth‑minded organizations actually want: a strategic partner who can turn technology into a lever for revenue, risk reduction, and scale. The good news is you’re already doing pieces of that work — you’re just not […]
Data as a Service: How MSPs Turn Noisy Logs into Business Insights

Small and mid‑sized businesses have more data than ever, but very little of it actually informs day‑to‑day decisions. Business intelligence (BI) platforms promise dashboards and data‑driven strategy, yet many SMEs either never deploy them fully, or they struggle with cost, complexity, and a lack of in‑house skills to make the tools pay off. Instead, executives […]
From “We Do Security” to Ransomware-Ready Compliance: How MSPs Turn Framework Jargon into Revenue and Risk Reduction
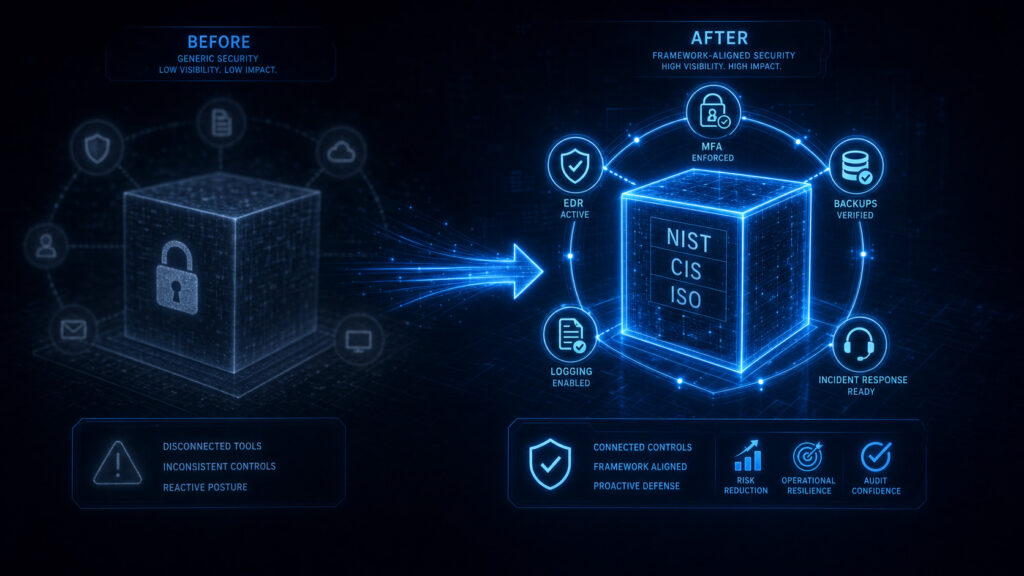
Buyers no longer accept “we do security” as an answer. They’re asking how security is implemented, whether it maps to recognizable frameworks, and if it is robust enough to satisfy insurers, auditors, and regulators when ransomware hits. This article walks through how to design a ransomware-ready stack that you can both operate and prove — […]
Important International Frameworks for Global MSPs (and What US-Only MSPs Need to Know)

Most managed service providers do not set out to become international compliance experts. Yet many already support clients with Canadian customers, UK subsidiaries, Australian operations, or financial-sector ties that bring unfamiliar regulatory frameworks into ordinary security conversations. What looks like a local MSP business can quickly become a cross-border risk problem when a prospect’s questionnaire […]
Incident Reporting Is Changing Faster Than Your Playbooks

For MSPs and internal IT teams, incident response used to revolve around containment, eradication, recovery, and a long argument over whether anyone outside the company really needed to know. That era is over. In the last two years, cyber incident reporting has shifted from a loosely coordinated mix of breach notice laws and sector rules […]
From Checkbox To Consequences: Why “Paper” Compliance Programs Are Now A Real Liability
MSPs and internal IT teams have spent years treating compliance as a documentation exercise: policies in SharePoint, audit binders on demand, screenshots gathered the night before a review, and a lot of confidence that “good enough” paperwork would carry the day. That model is breaking down. In 2026, regulators are signaling that they expect organizations […]
Mythos, Vendor Risk, and the Supply Chain Problems MSPs Can’t Ignore

If the Mythos supply chain incident felt like somebody else’s problem, that feeling did not last long. The useful lesson for MSPs is not that one AI-related event made headlines, but that it exposed how quickly upstream vendor failures, weak access controls, and murky fourth-party relationships can become downstream operational risk for service providers and […]
