OAuth Abuse Is the New Phishing: Why “Log In With X” Keeps Burning You
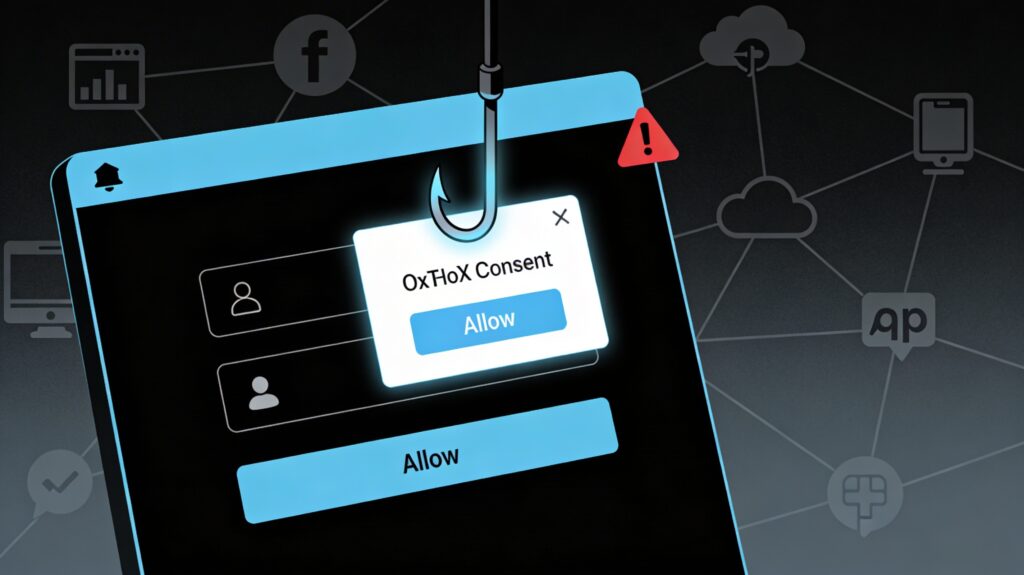
OAuth abuse has quietly become the phishing technique that slips past your MFA, your “security‑aware” users, and your cloud email filters. Recent campaigns abusing OAuth redirects and malicious apps in Microsoft Entra ID and Google Workspace show that “Log in with X” is now one of the easiest ways into your SaaS estate. Phishing Without […]
The New Breach Supply Chain: When Your Data Broker Gets Pwned
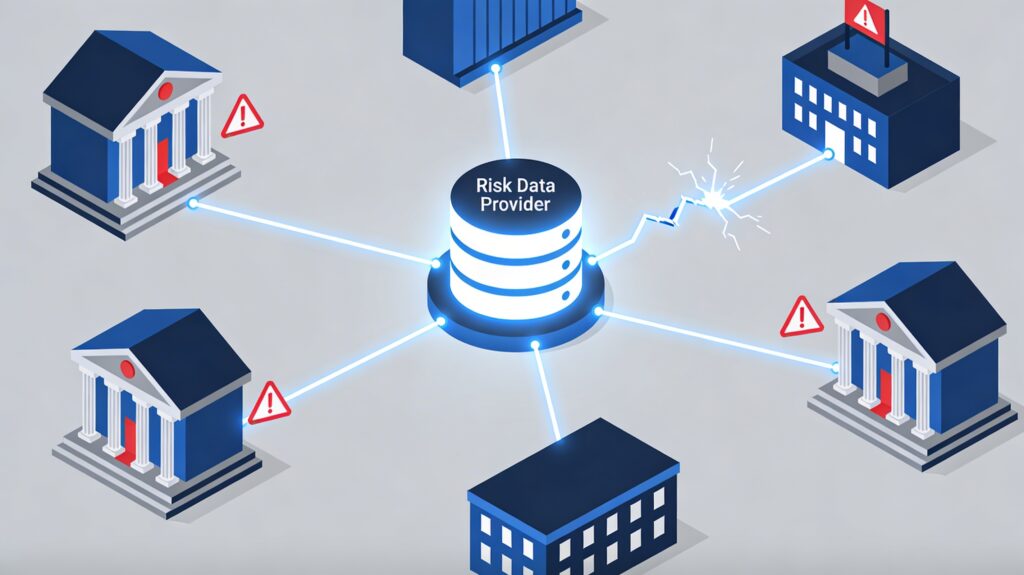
When your supply chain gets breached, you inherit its chaos, whether you like it or not. The LexisNexis incident and a wave of third‑party breaches in 2026 are a warning shot for every legal, risk, and engineering leader who leans on data brokers to keep their business compliant and fraud‑resistant. When Your Data Provider Makes […]
